This article describes step by step how I installed Active Directory Domain Services (AD DS) and DNS on a Windows Server 2022 Datacenter VM in a VMware Fusion lab environment. The result is a fully functional domain controller for the domain lab.local, serving as the foundation for a Windows DevOps lab.
Environment
| Component | Value |
|---|---|
| Virtualization | VMware Fusion (macOS) |
| Guest OS | Windows Server 2022 Datacenter (Desktop Experience) |
| Hostname | DC01 |
| Domain name | lab.local |
| NetBIOS name | LAB |
| Lab network adapter | Ethernet1 — 172.16.37.10 (static IP) |
| Internet adapter | Ethernet0 — DHCP via VMware NAT |
Step 1 — Configure Networking
Before installing Active Directory, the domain controller needs a static IP address. AD DS and DNS depend on a stable address.
The VM has two network adapters: one for internet access (NAT, DHCP) and one for the lab network (Private to my Mac, static IP).
1.1 Add a Second Network Card in VMware Fusion
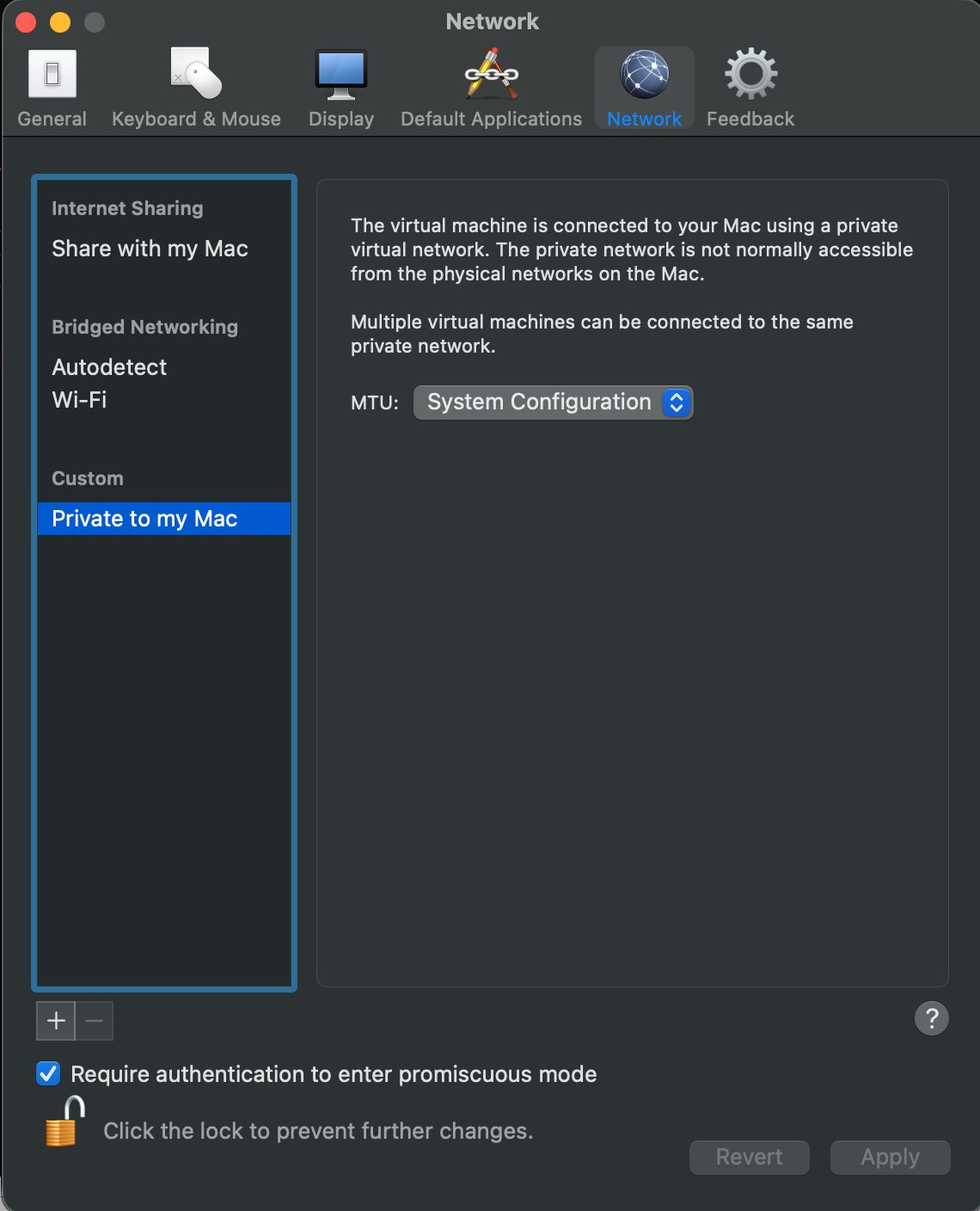
The VM must be powered off to add a second network adapter. Go to VM > Settings and add a new Network Adapter. Set it to Private to my Mac.
1.2 Set a Static IP on Ethernet1
Open Control Panel > Network Connections. Right-click Ethernet1 > Properties > Internet Protocol Version 4 (TCP/IPv4) > Properties.
Fill in the following values:
- IP address:
172.16.37.10 - Subnet mask:
255.255.255.0 - Default gateway: leave empty
- Preferred DNS server:
172.16.37.10(DC01 points to itself)
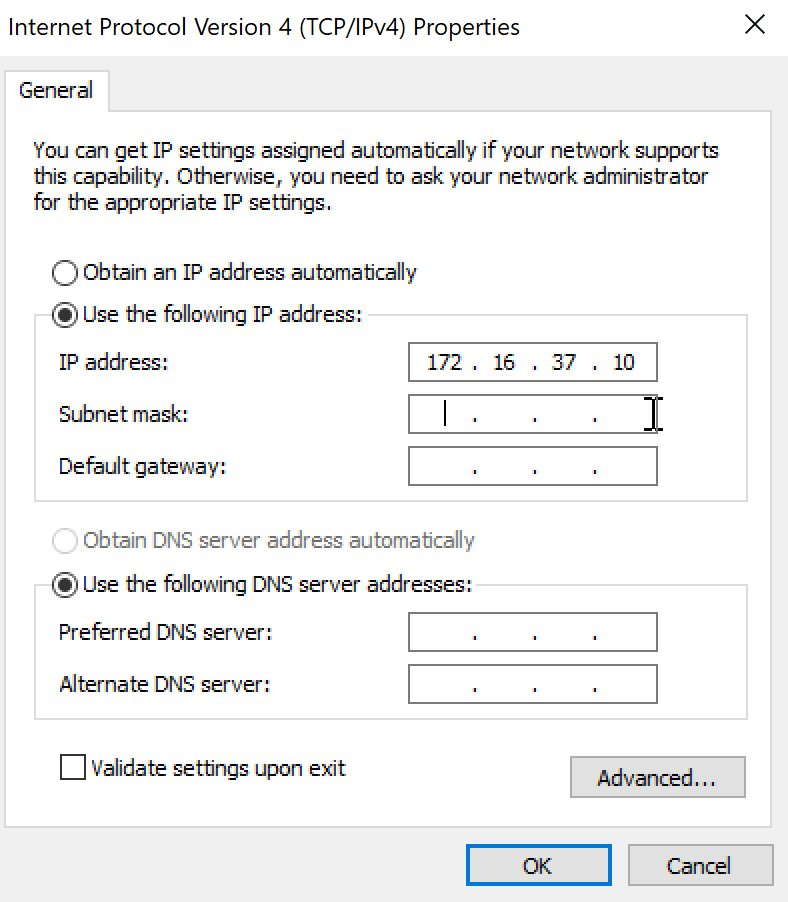
Note: Ethernet0 (internet) stays on DHCP. Only Ethernet1 gets a static IP. This way the VM works anywhere — at home, at work, at a relative’s place — because the internal lab network is completely isolated.
1.3 Verification
Open PowerShell and verify:
1Get-NetIPAddress -AddressFamily IPv4 | Select-Object InterfaceAlias, IPAddress
Expected output:
1Ethernet1 172.16.37.10
2Ethernet0 192.168.x.x (varies via DHCP)
Step 2 — Install the AD DS Role via Server Manager
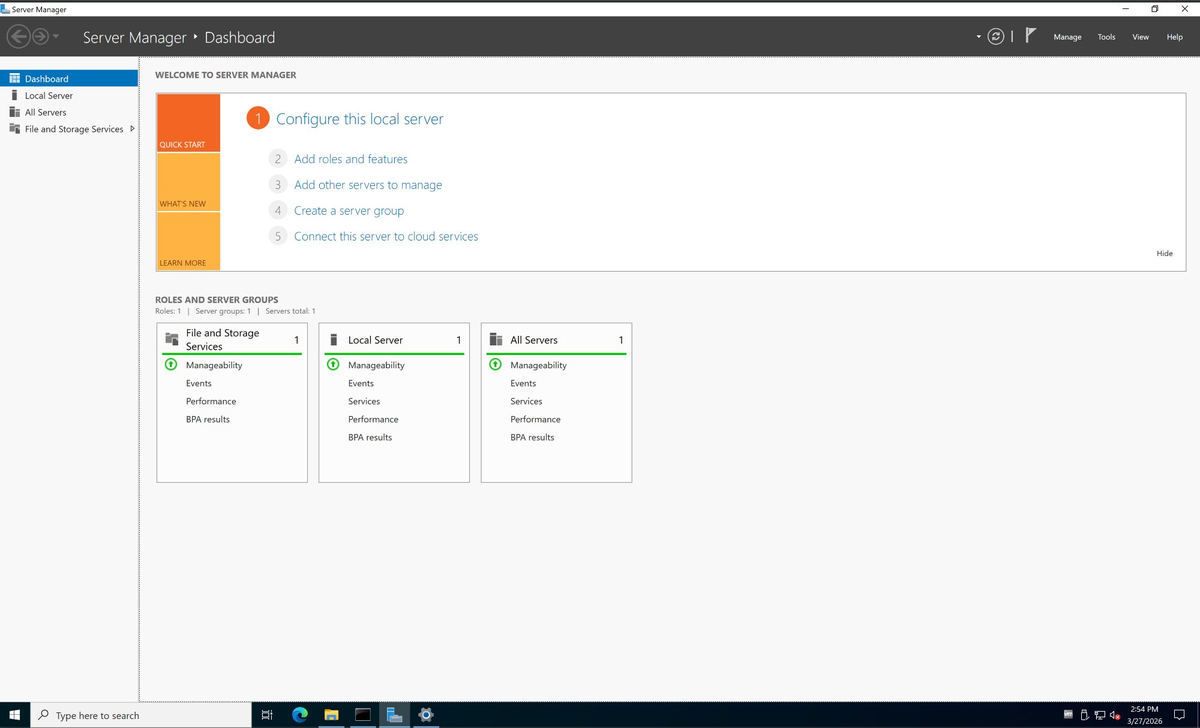
2.1 Open Server Manager
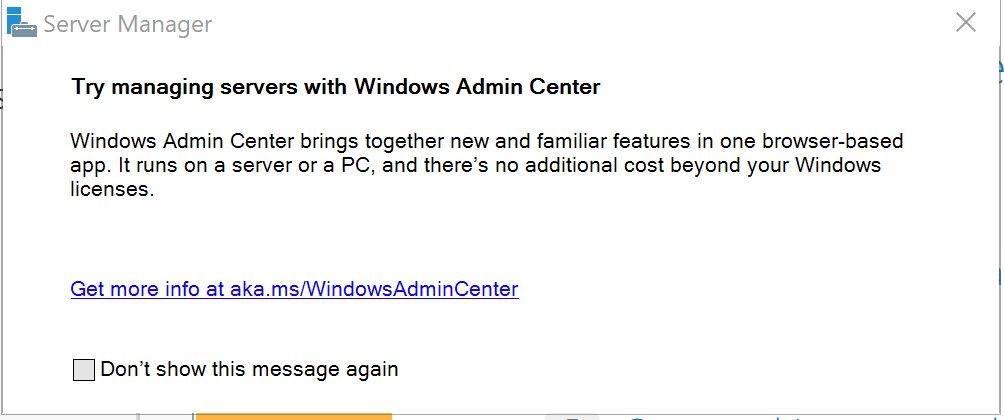
Server Manager opens automatically after login. Dismiss the Windows Admin Center notification.
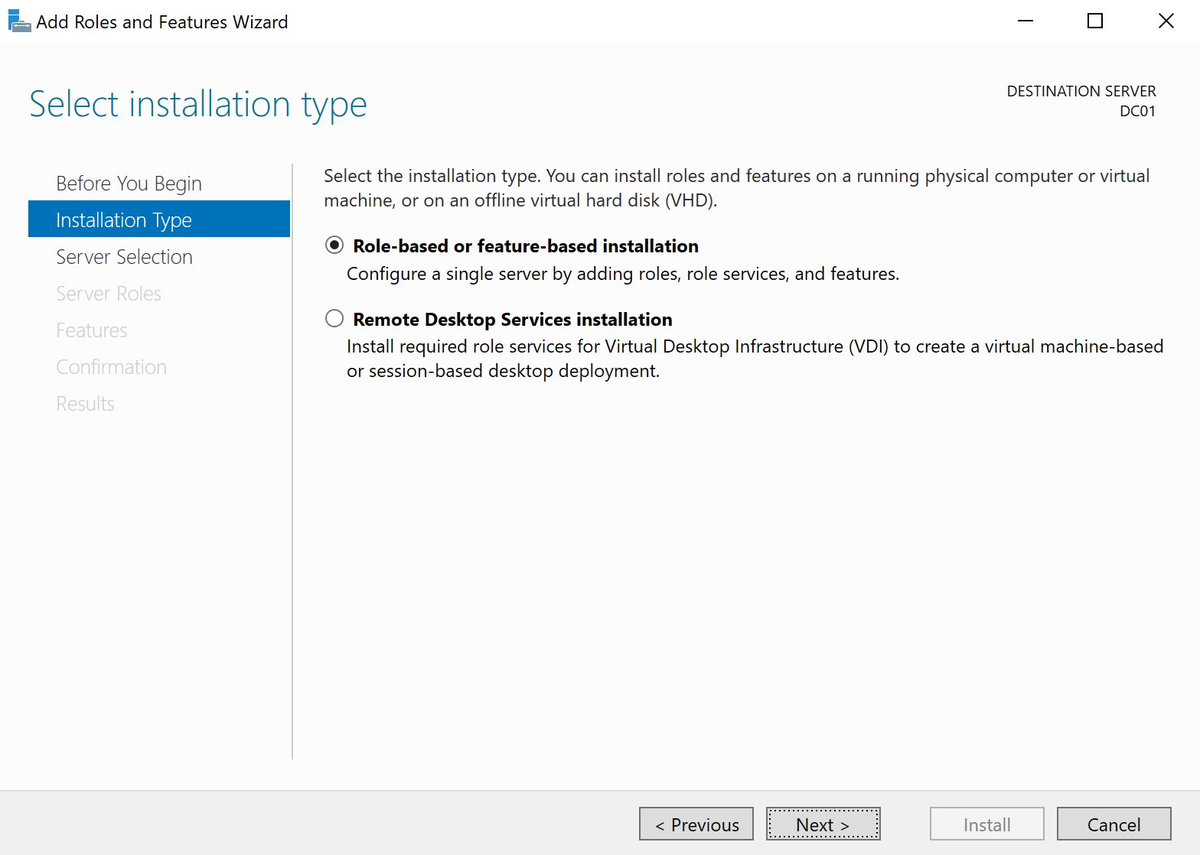
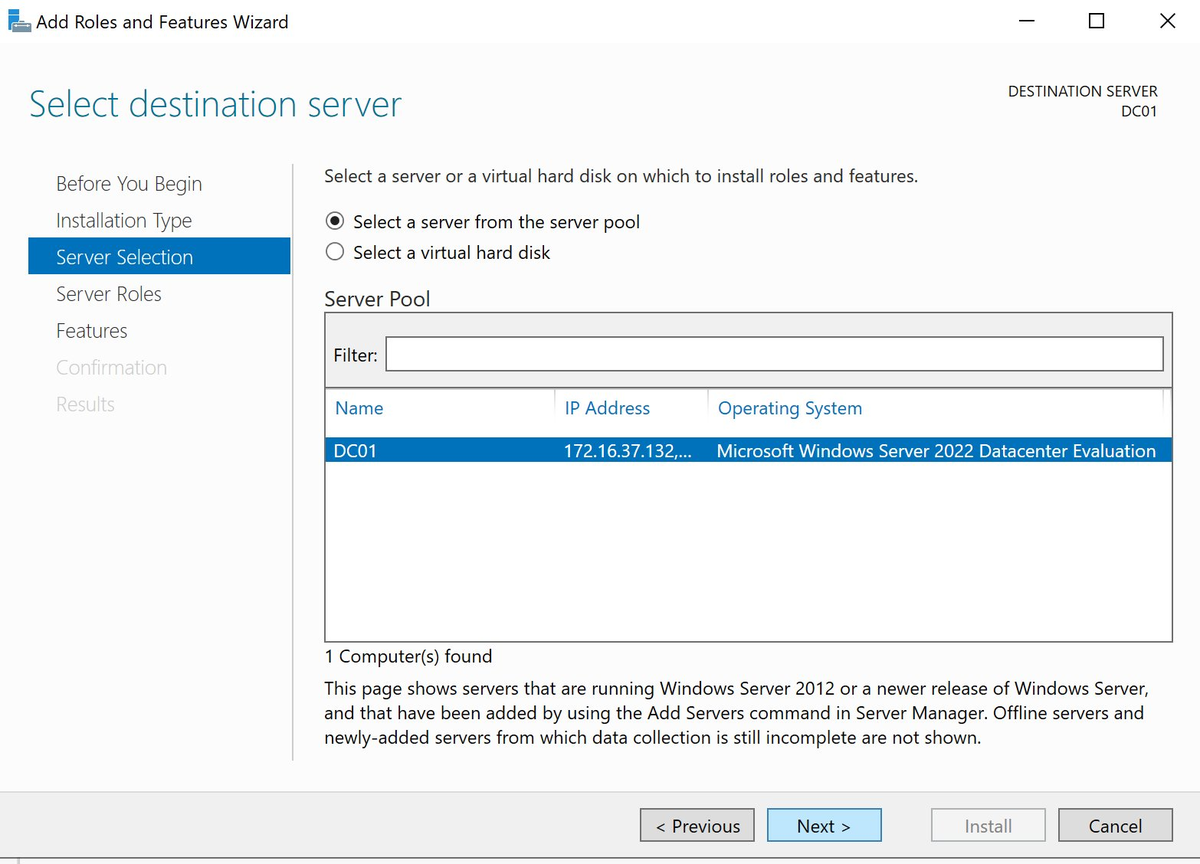
2.2 Add a Role
Click Add roles and features in the Dashboard.
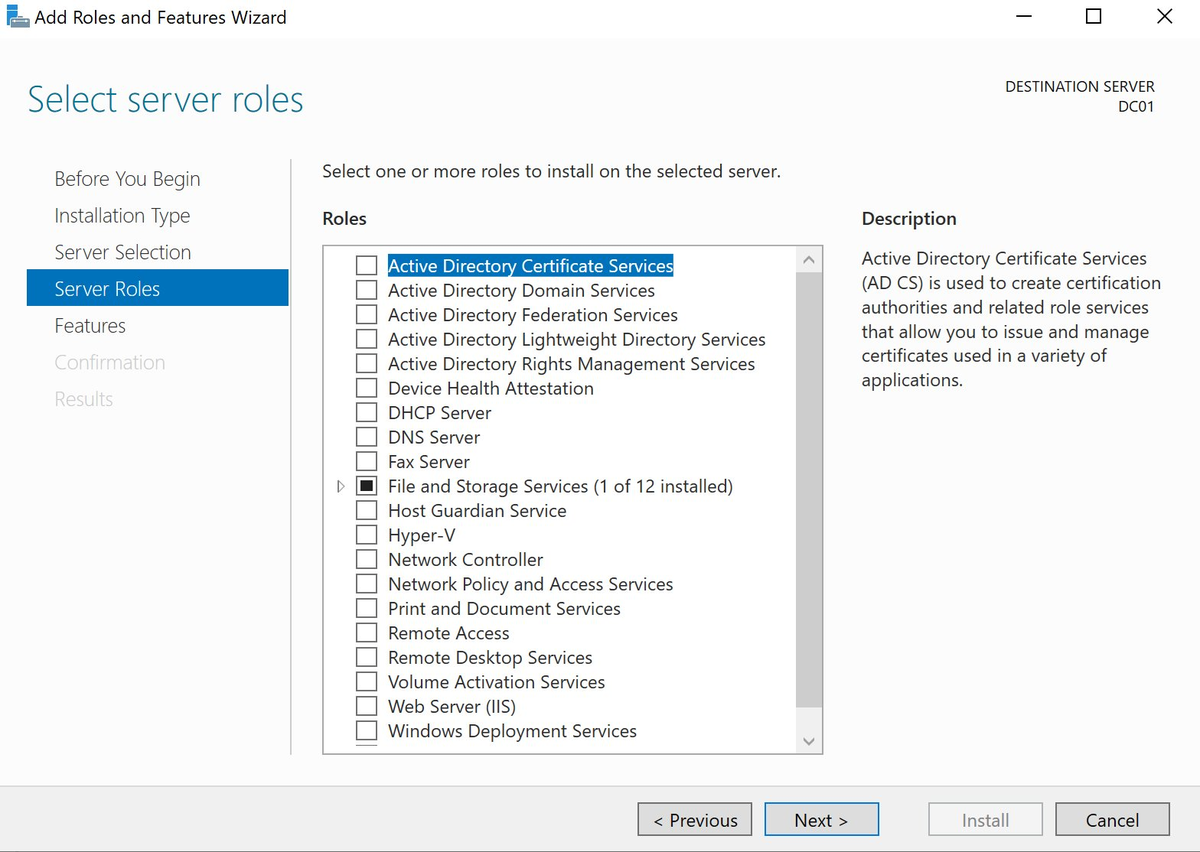
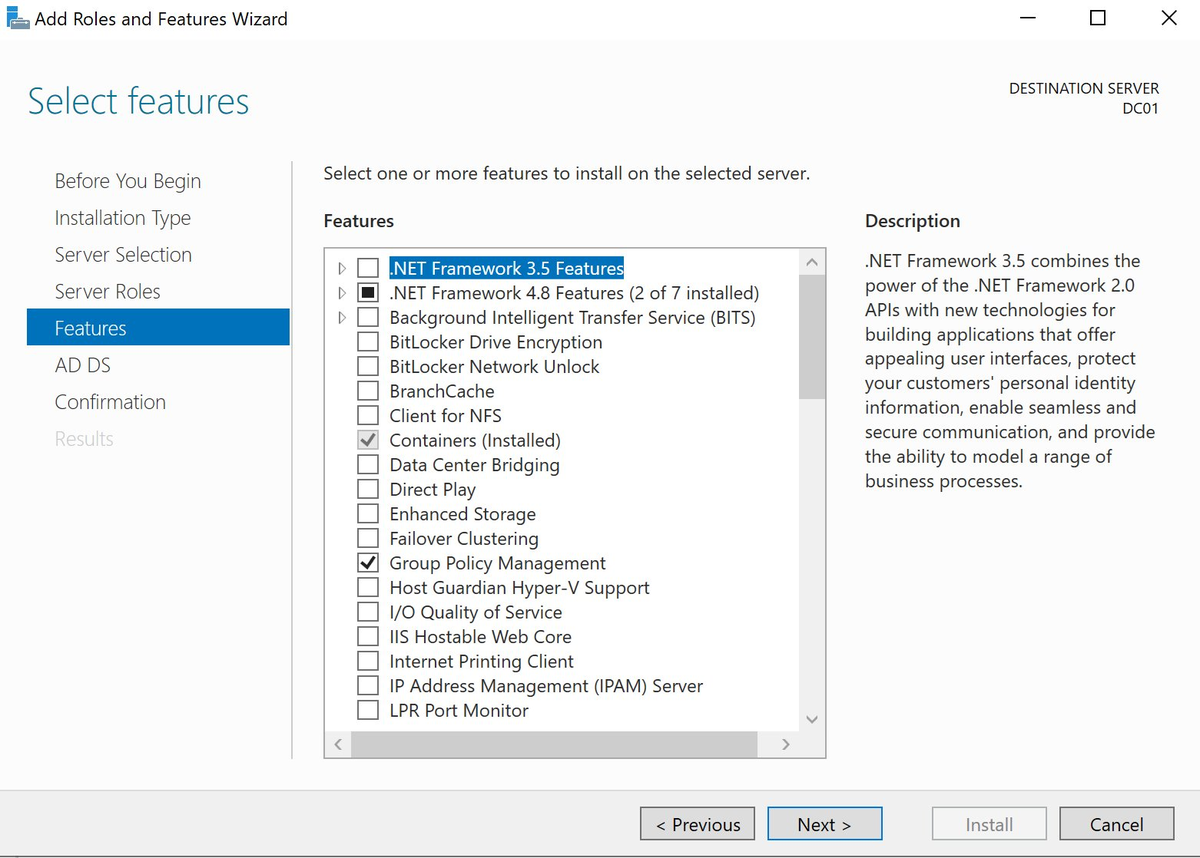
2.3 Select Active Directory Domain Services
Check Active Directory Domain Services. A popup will appear asking to add required features — click Add Features.
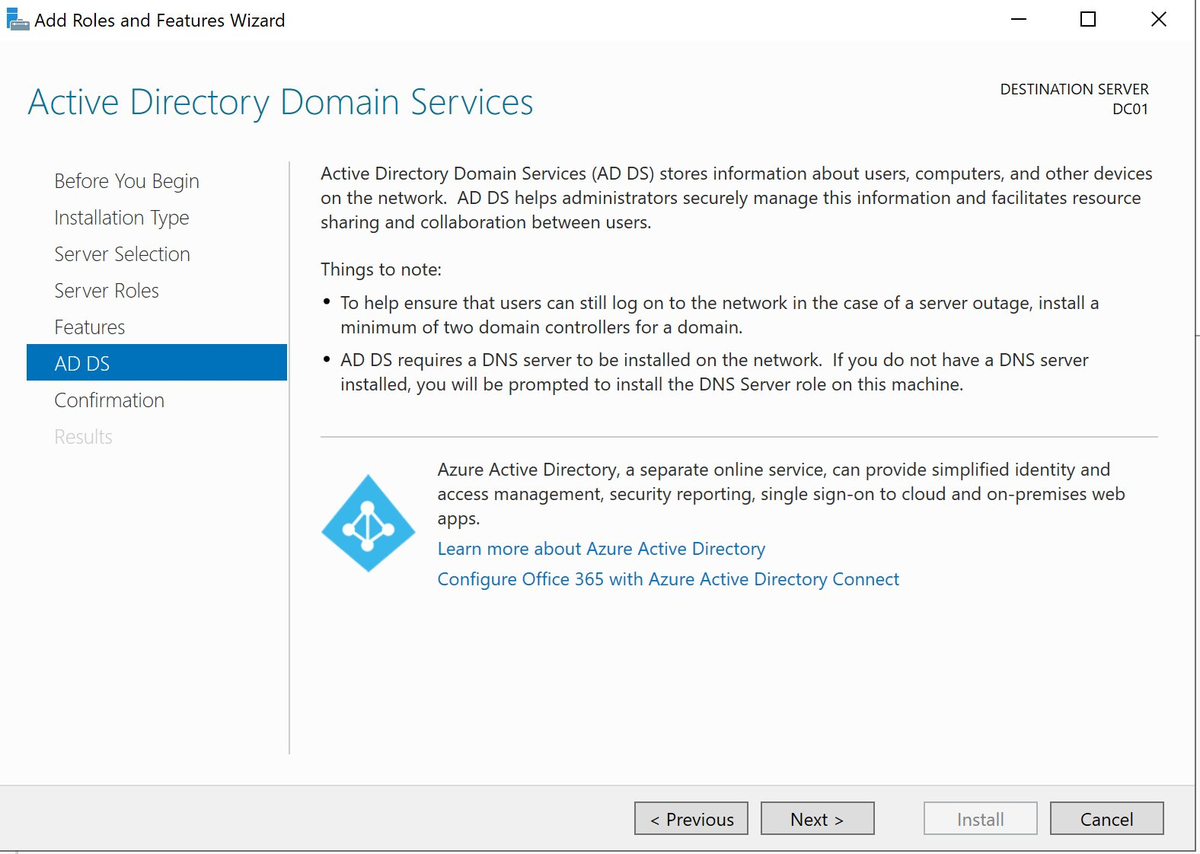
2.4 AD DS Information Page
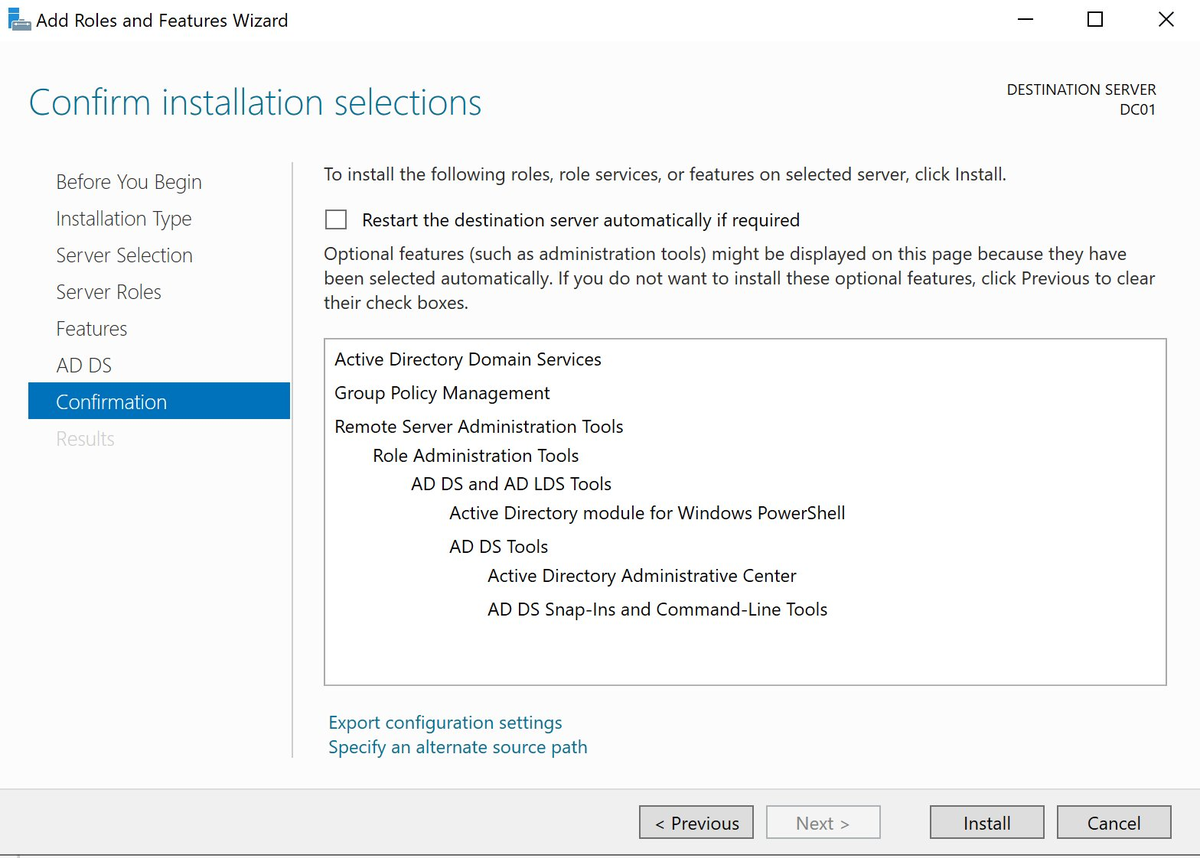
2.5 Confirm Installation
Check Restart the destination server automatically if required and click Install.
2.6 Installation Successful
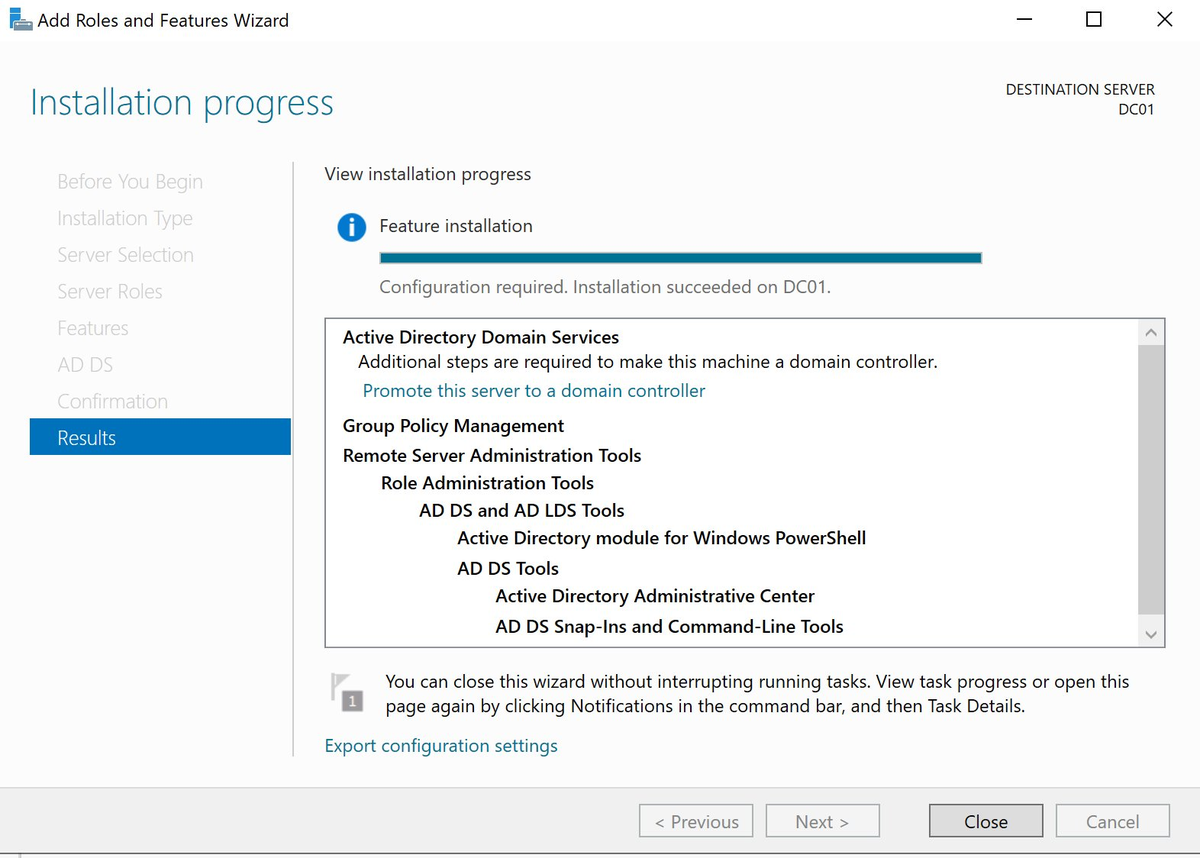
Important: The AD DS role is now installed but DC01 is not yet a domain controller. The link “Promote this server to a domain controller” is the next step.
Step 3 — Configure the Domain Controller
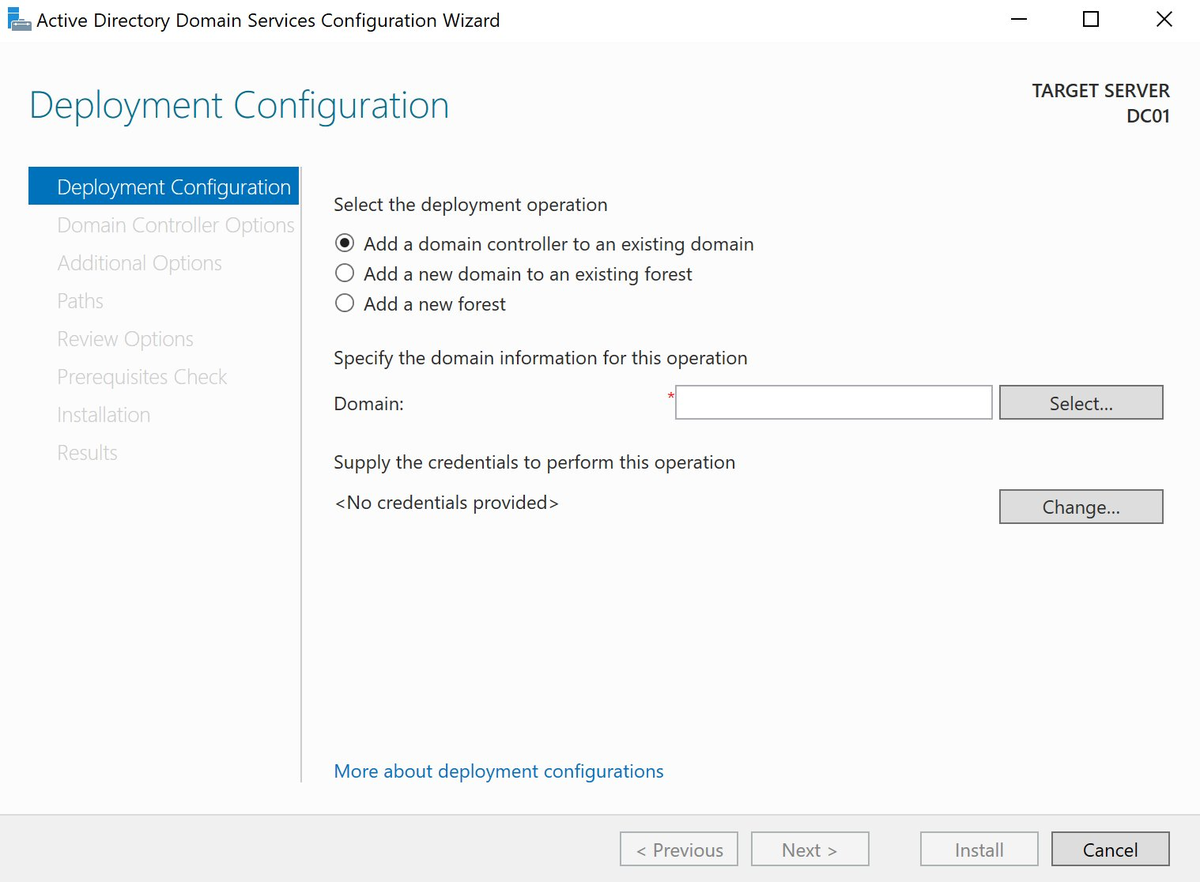
3.1 Deployment Configuration
Choose Add a new forest and enter as Root domain name: lab.local
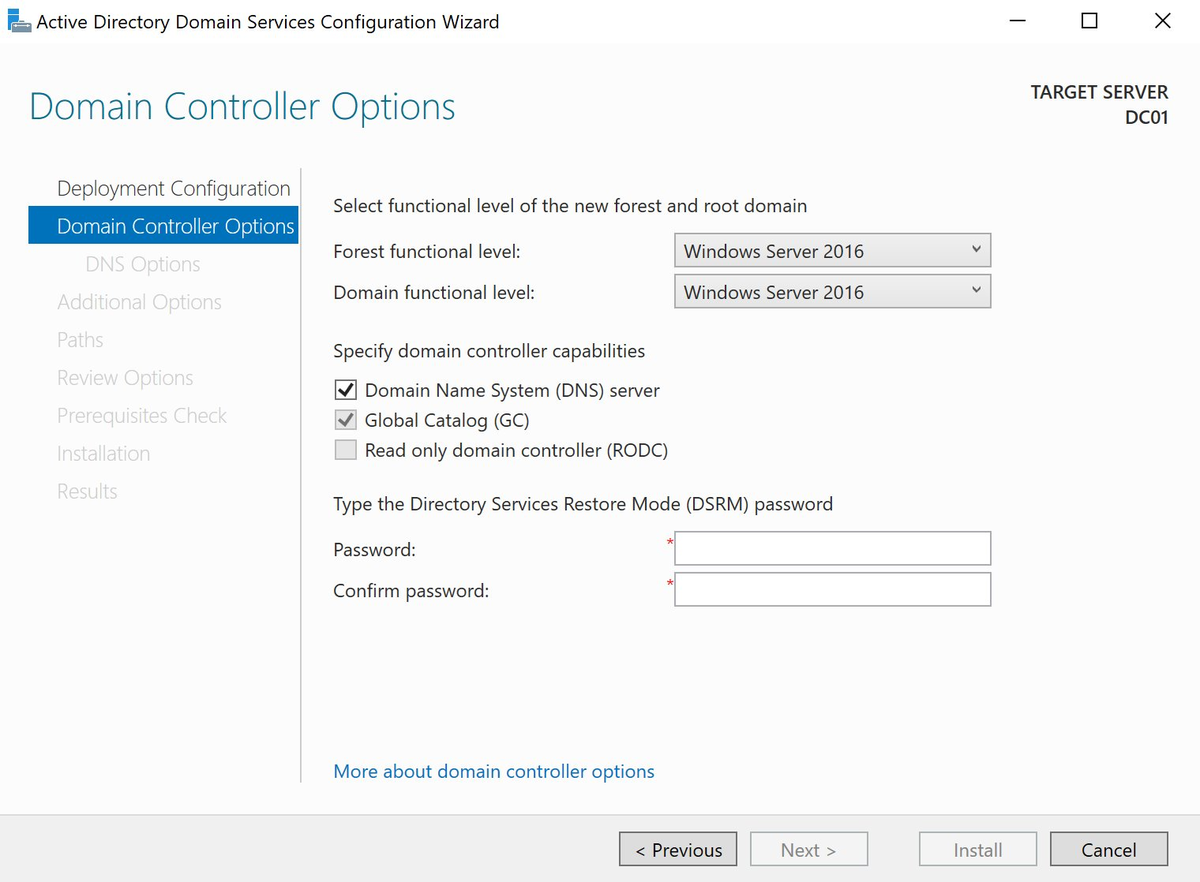
3.2 Domain Controller Options
Functional levels are set to Windows Server 2016 — fine for a modern lab. DNS server and Global Catalog are checked.
Set the DSRM password. This is an emergency password for Active Directory recovery — store it safely.
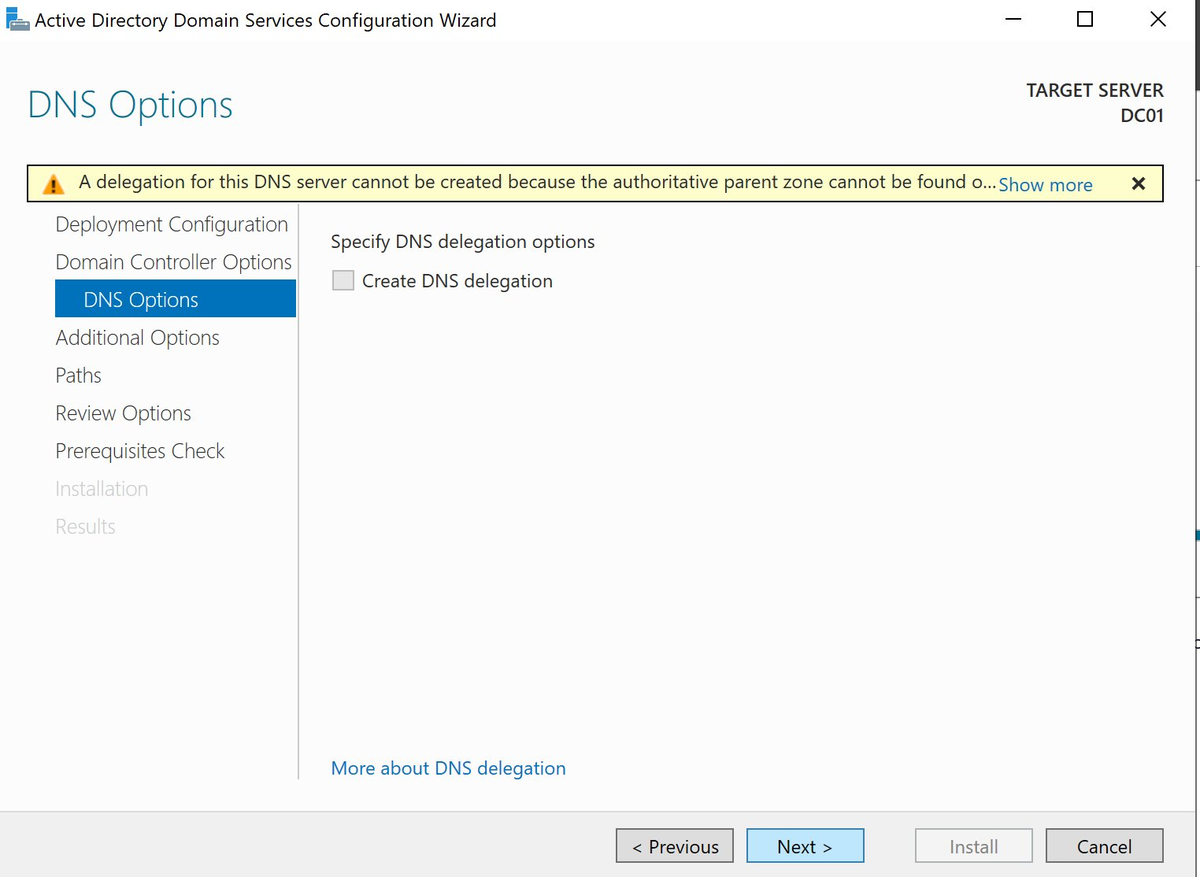
3.3 DNS Options
A warning appears that a DNS delegation cannot be created. This is normal for an internal lab domain like lab.local that doesn’t exist on the public internet. Leave Create DNS delegation unchecked.
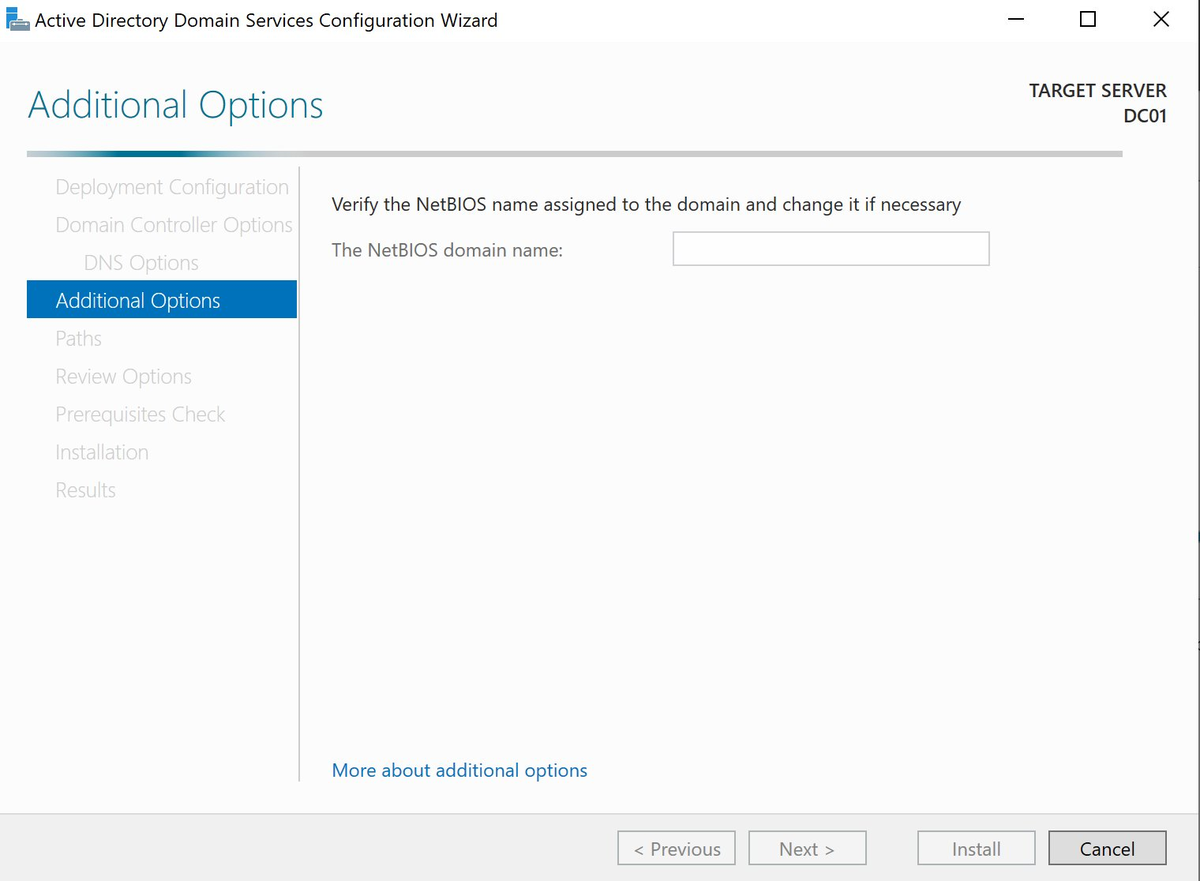
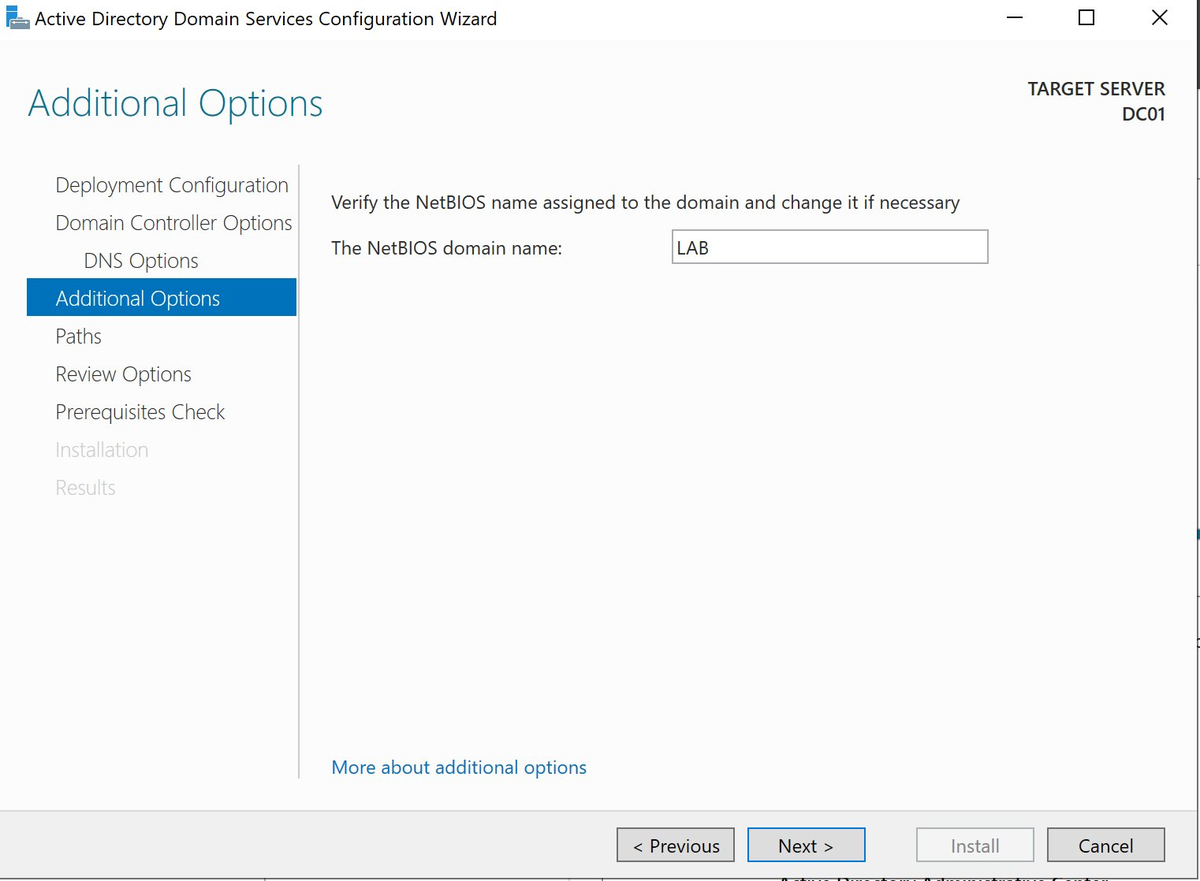
3.4 NetBIOS Name
Windows automatically sets the NetBIOS name to LAB. Wait for the field to populate.
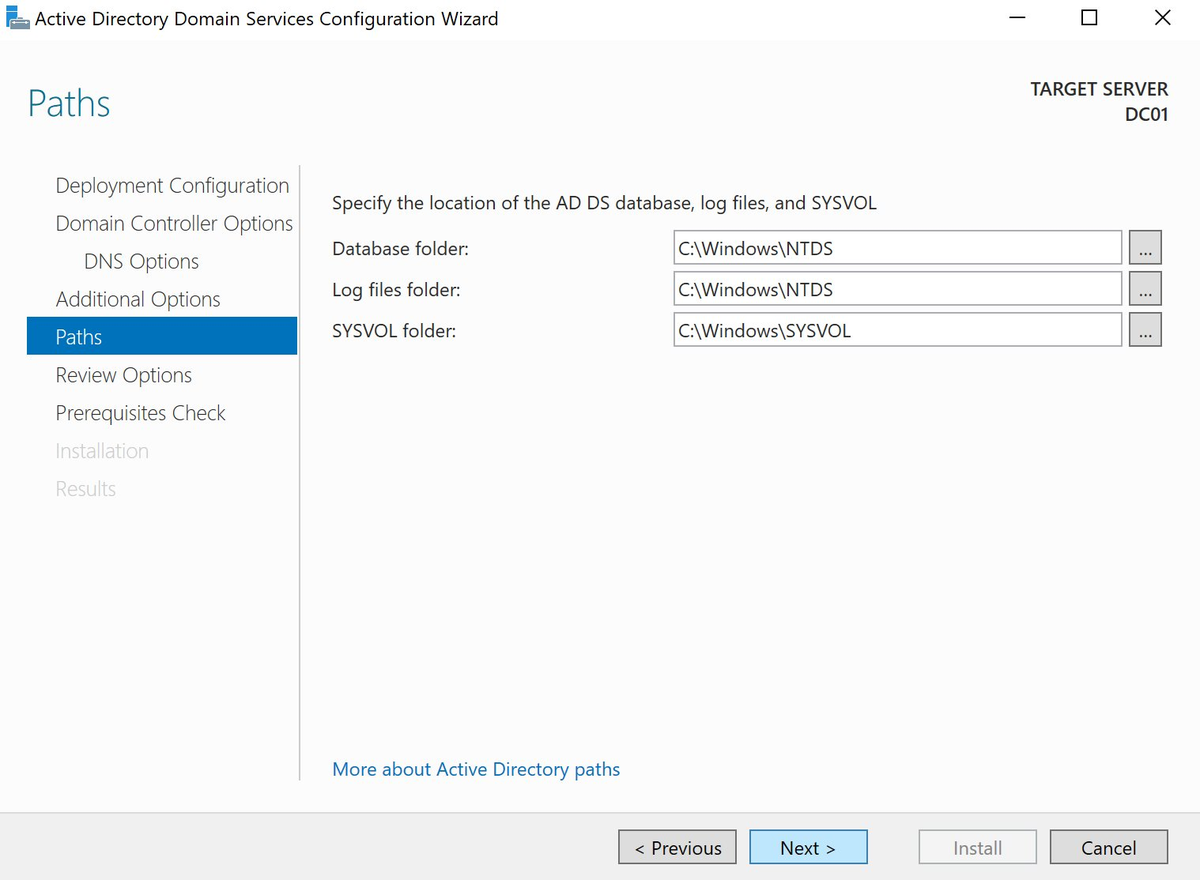
3.5 File Locations
The default locations are fine for a lab.
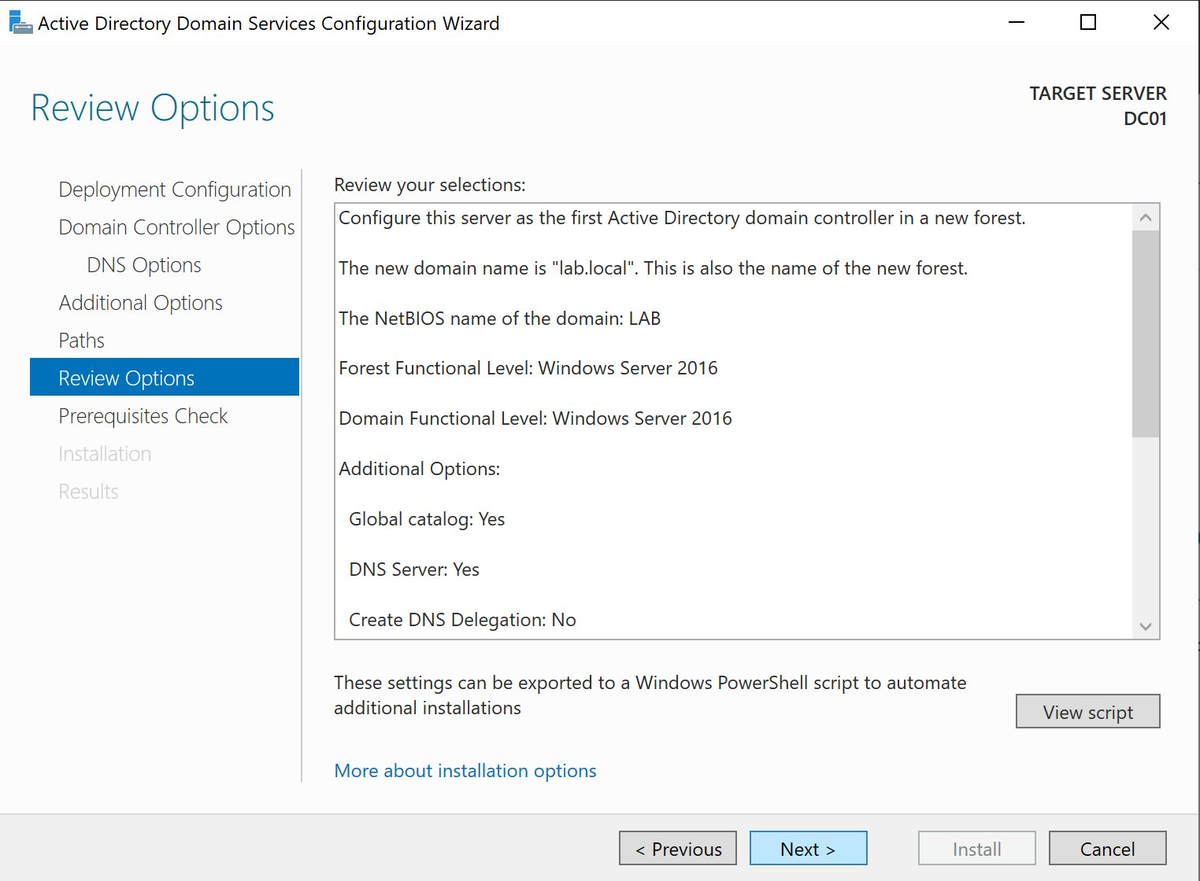
3.6 Review Options
Verify the summary:
- Domain:
lab.local - NetBIOS:
LAB - DNS Server: Yes
- Global Catalog: Yes
- Create DNS Delegation: No
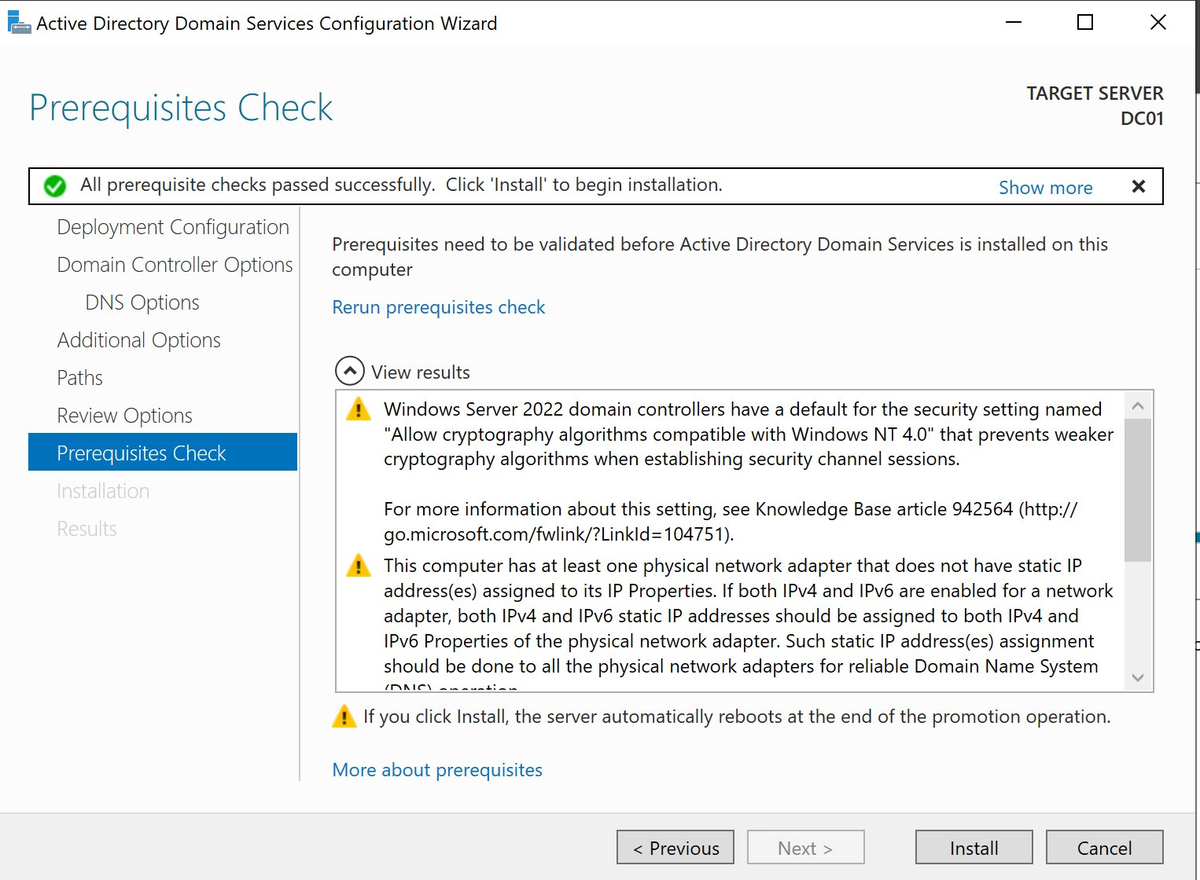
3.7 Prerequisites Check
The green checkmark confirms all checks have passed. Yellow warnings are normal for a lab.
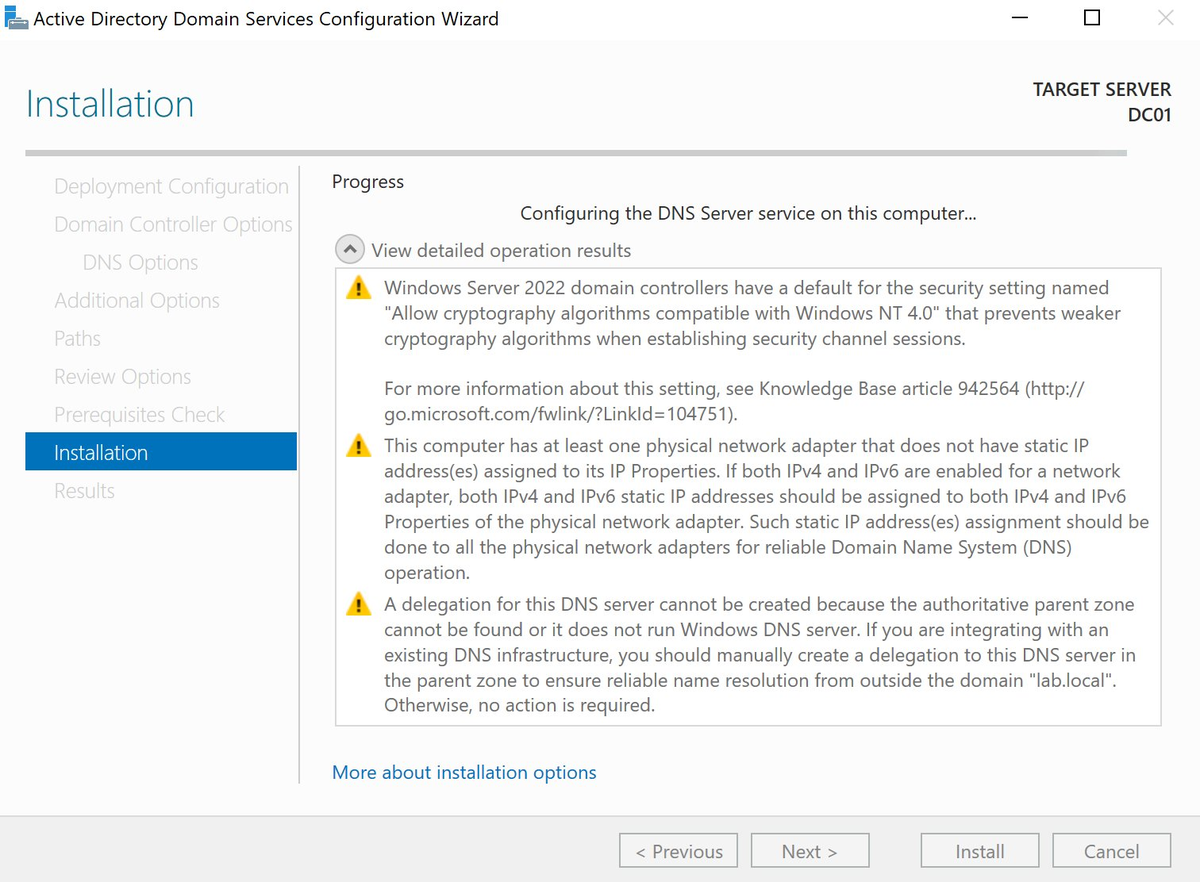
3.8 Installation
The server configures DNS and restarts automatically.
After the reboot: Log in as
LAB\Administratorinstead of the local Administrator.
Step 4 — Verification After Installation
Open PowerShell as Administrator and verify:
1# Domain information
2Get-ADDomain
3
4# Domain controller information
5Get-ADDomainController
6
7# Check DNS zones
8Get-DnsServerZone
9
10# Test name resolution
11Resolve-DnsName dc01.lab.local
If Resolve-DnsName dc01.lab.local returns IP address 172.16.37.10, DNS is working correctly.
Next Steps
Now that DC01 is functioning as a domain controller for lab.local, the next steps are:
- CA01 — Certificate Authority for internal TLS certificates (Jenkins, Harbor, Nexus)
- Join other VMs to lab.local — point DNS to
172.16.37.10on each new VM - Create Organisational Units and service accounts for Jenkins, Ansible and Nexus

Comments